Different ways devices are added to Entra ID and Intune
How to tell the difference
1/27/20262 min read
How to understand the different ways devices are added to Entra ID and Intune (Registered vs Joined)
Many Intune and Entra administrators troubleshoot device issues without fully understanding how a device was added to Entra ID and Intune—and that misunderstanding often leads to incorrect policies, broken Conditional Access, and failed enrollments.
What this guide covers
• The different device states in Microsoft Entra ID
• How each device type interacts with Microsoft Intune
• When to use Registered, Joined, or Hybrid Joined devices—and when not to
The four main device states you need to understand
Before touching policies or troubleshooting, you need to identify how the device exists in Entra ID. This determines identity trust, token issuance, and management capabilities.
1. Entra ID Registered (Azure AD Registered)
What it is
A personally owned device that is registered to a user, not the organization.
Typical scenarios
• BYOD Windows devices
• iOS / Android devices enrolled with user sign-in
• macOS personal devices
Key characteristics
• Device has a user-based identity only
• No computer account in Entra ID
• Limited Conditional Access signals
• Often paired with MAM (App Protection Policies)
Remeber that:
• Registered ≠ managed
• Registered devices can exist without Intune enrollment
• Device-based Conditional Access is limited
When useful:
• BYOD strategies
• App-level protection without full device control
2. Entra ID Joined (Azure AD Joined)
What it is
A corporate-owned device joined directly to Entra ID and fully trusted.
Typical scenarios
• Windows 10/11 cloud-native devices
• Autopilot deployments
• Kiosk or shared devices
Key characteristics
• Device has its own Entra ID identity
• Full support for device-based Conditional Access
• Deep integration with Intune
• No on-prem Active Directory dependency
Remember that:
• Join happens during OOBE or Settings → Accounts
• Requires Entra ID join rights
• Ideal for Zero Trust architectures
When useful
• Modern, cloud-first Windows environments
3. Hybrid Entra ID Joined (Hybrid Azure AD Joined)
What it is
A device joined to on-prem Active Directory and registered in Entra ID.
Typical scenarios
• Legacy Windows environments
• Organizations transitioning from AD to Entra ID
• Devices managed by GPO + Intune
Key characteristics
• Two identities: on-prem AD + Entra ID
• Requires line-of-sight to domain during join
• More complex troubleshooting
• Often slower policy evaluation
Remember that:
• Hybrid join is not instant
• Device writeback and SCP configuration are critical
• Most common source of “device not compliant” CA issues
When useful:
• Transitional environments with AD dependency
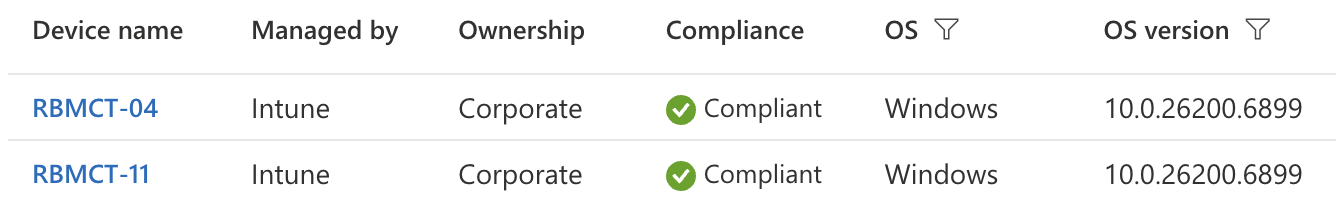
4. Entra ID Joined + Intune Enrolled (The Managed State)
What it is
This is not a separate join type—but the desired end state.
A device can be:
• Entra ID Joined and
• Enrolled into Intune (MDM)
Why this matters
• Entra ID handles identity and trust
• Intune handles management and compliance
• Conditional Access evaluates both
Remeber that:
A device can be:
• Joined but not managed
• Managed but not compliant
• Compliant but not targeted correctly
Understanding this separation prevents most troubleshooting mistakes.
How device state affects Conditional Access
Conditional Access does not ask “Is this device healthy?”
It asks:
• Is the device known to Entra ID?
• Is it managed by Intune?
• Is it compliant at evaluation time?
Common mistake (and why it causes issues)
Mistake:
Assuming that “the device exists in Entra ID, so Intune and CA will work.”
Reality:
• Entra ID = identity
• Intune = management
• Compliance = evaluation result
Each is independent and evaluated separately.
This is why:
• Devices show as Managed but still fail CA
• “Device not compliant” appears unexpectedly
• Policies never apply despite successful enrollment
Summary
• Registered devices are user-owned and limited
• Entra ID Joined devices are corporate and trusted
• Hybrid Joined devices add complexity and legacy dependencies
• Intune enrollment is a separate but critical step
• Conditional Access evaluates identity + management + compliance
Understanding these differences will eliminate a large percentage of Intune and Entra troubleshooting scenarios before they even start.
Go 4 IT ! 😀